-
Courses

Courses
Choosing a course is one of the most important decisions you'll ever make! View our courses and see what our students and lecturers have to say about the courses you are interested in at the links below.
-
University Life

University Life
Each year more than 4,000 choose University of Galway as their University of choice. Find out what life at University of Galway is all about here.
-
About University of Galway

About University of Galway
Since 1845, University of Galway has been sharing the highest quality teaching and research with Ireland and the world. Find out what makes our University so special – from our distinguished history to the latest news and campus developments.
-
Colleges & Schools

Colleges & Schools
University of Galway has earned international recognition as a research-led university with a commitment to top quality teaching across a range of key areas of expertise.
-
Research & Innovation

Research & Innovation
University of Galway’s vibrant research community take on some of the most pressing challenges of our times.
-
Business & Industry

Guiding Breakthrough Research at University of Galway
We explore and facilitate commercial opportunities for the research community at University of Galway, as well as facilitating industry partnership.
-
Alumni & Friends

Alumni & Friends
There are 128,000 University of Galway alumni worldwide. Stay connected to your alumni community! Join our social networks and update your details online.
-
Community Engagement

Community Engagement
At University of Galway, we believe that the best learning takes place when you apply what you learn in a real world context. That's why many of our courses include work placements or community projects.
How to Spot Phishing Emails

You can protect yourself from phishing attacks by taking the initial step of learning how to spot a phishing email. There are a number of typical warning signs to look out for including bad grammar, an urgent action required, incomplete or fake contact details or information. These can all be signs that something is wrong and alert you to a phishing attack. If you are ever unsure of an email then proceed with caution. Never click on any links or open any attachments on a suspicious email.
If you think that you have received a phishing email you can report it by forwarding the email to phishing@nuigalway.ie and our IT team can take the appropriate steps in blocking the email.
See the below examples of typical phishing emails that would be sent to staff or students in NUI Galway:
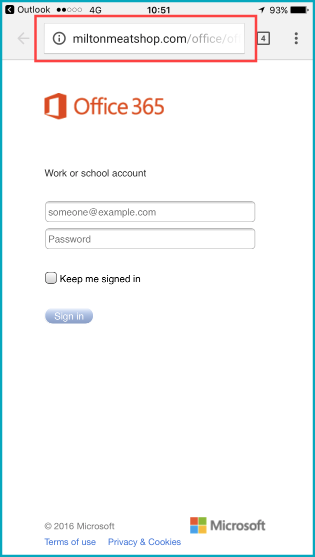
Example 1: Validate Campus Account
- ISS will never ask you to verify any of your information over email
- Asking you to go to an external link, you can check where this link will bring you by hovering over the link. You can see that the address for this link has nothing to do it with what it is pretending to be
- Incorrect sign-off, “NUI IT Helpdesk”. Our name is the “NUIG ISS Service Desk”
Example 2: Order Confirmation Invoice / Spoofing
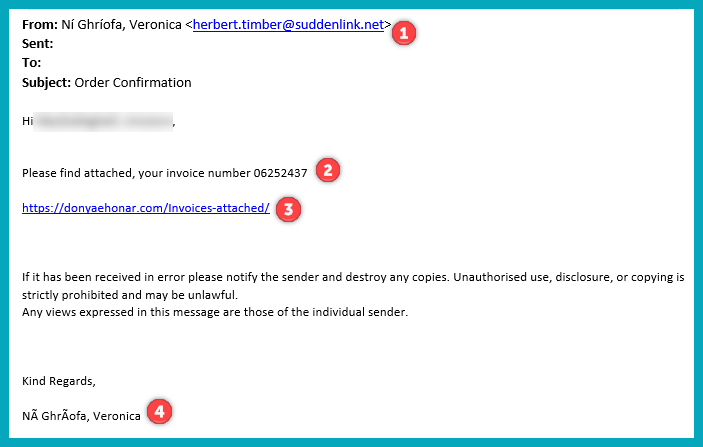
- Spoofing email address, we can see that the display name does not match the email address name
- Invoice or payment that you did not make, suspicious company name
- Asking you to go to a link with a suspicious name, or one you have never heard of before
- Spelling/Grammar mistakes, the sign off name is spelt incorrectly or has unrecognised characters
Example 3: Delete Email Account
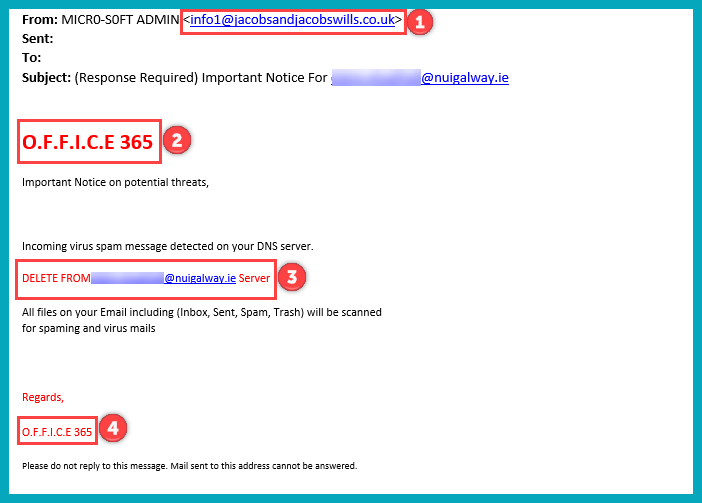
- Suspicious email address
- Incorrect logo used
- Sense of Urgency, informing that account will be deleted within a certain amount of time
- Incorrect logo used again
Example 4: Invoice Attached
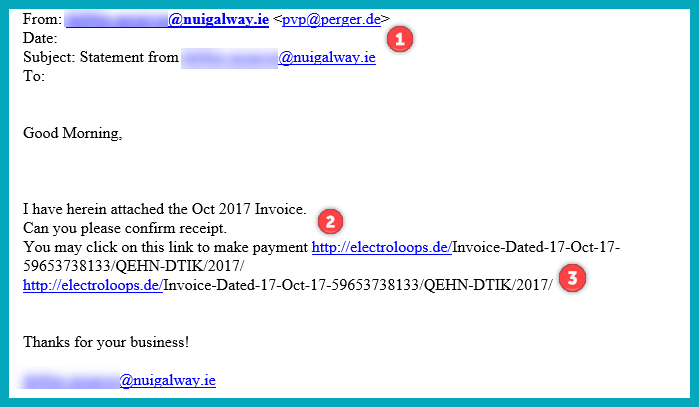
- Suspicious email address
- Invoice or payment that you did not make, suspicious company name
- Asking to go to external link, the URL is suspicious
Example 5: Email Storage Exceeded
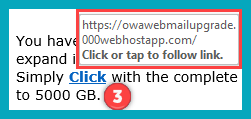
- Unrecognised email address
- Sense of Urgency, informing that account will be deleted within a certain amount of time
- Asking to go to external link, when hovered over you can see that the URL is suspicious
Example 6: File Tax Return
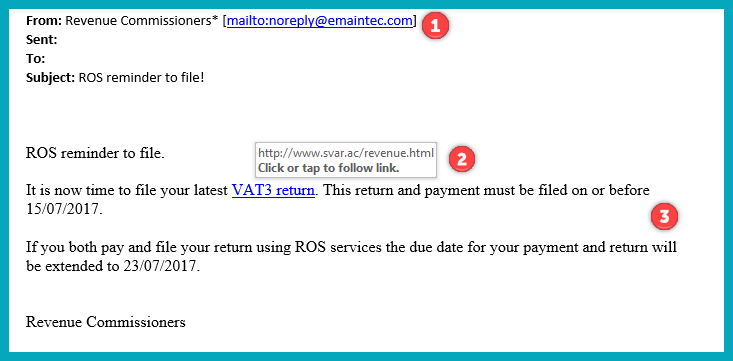
- Suspicious email address
- Sense of Urgency, asking for payment within a certain amount of time
- Asking to go to external link, when hovered over you can see that the URL is suspicious
Example 7: PayPal Payment
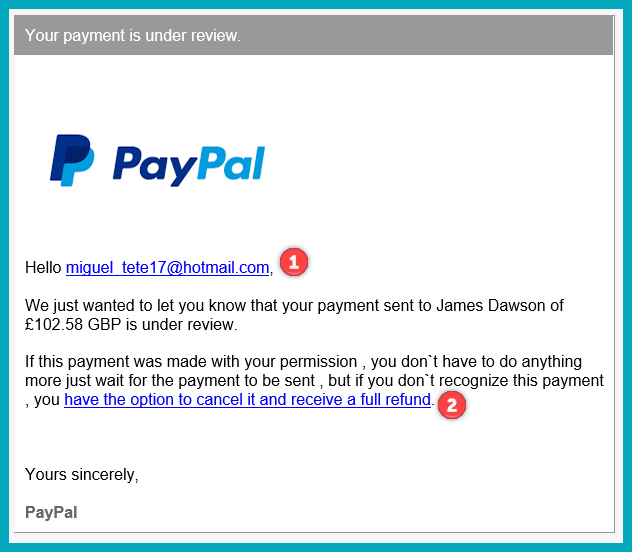
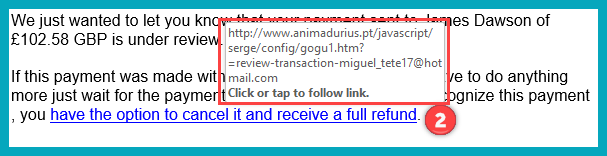
- Address you by email address instead of actual First Name, Last Name.
- Asking to go to external link, when hovered over you can see that the URL is suspicious
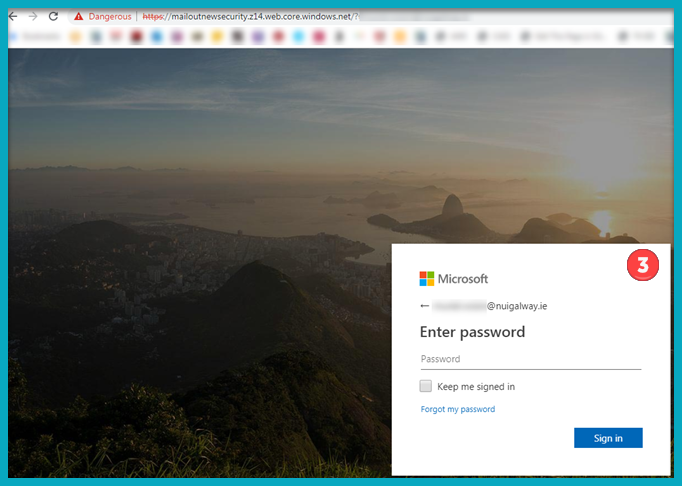
Example 8: Convincing Phishing Sites
Some phishing attempts can be very convincing but it is always very important to make sure that you check all key aspects before continuing. This site has a spoofed URL which has nothing to do with the site which tells us that it is a phishing attempt.
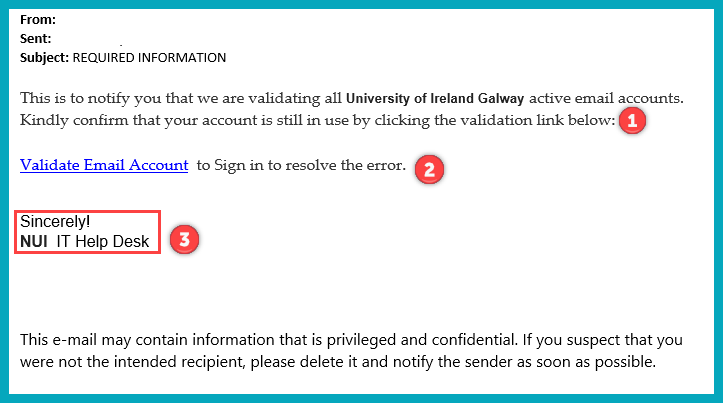
Example 9: Revalidate Your Email Account

- Unusual and unrecognised email address. Email address doesn’t match with the sign off of the email, “Technical help desk”
- Information Solutions and Services (ISS) DO NOT and WILL NEVER request details of your password by email or ask you if your account is still in use via email. If you receive a message asking for your email account details, delete it without response.
- Email is signed off as “Technical help desk”. This is not a department of the college, our name is Information Solutions and Services (ISS).
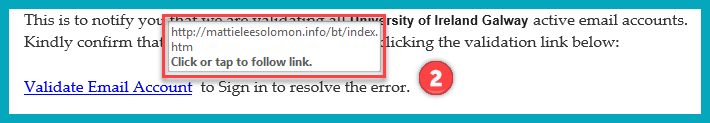
Example 10: Request to Update Account Details
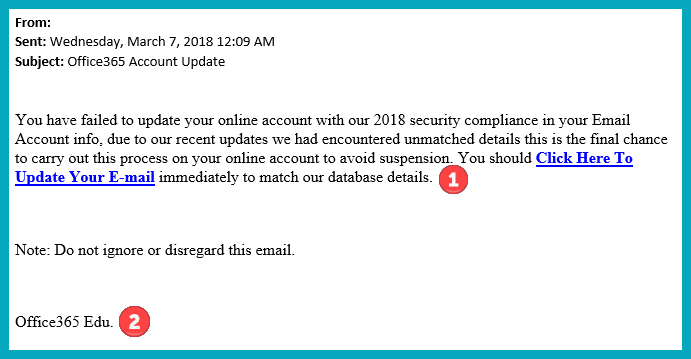
- Information Solutions and Services (ISS) DO NOT and WILL NEVER request details of your password by email or ask you if your account is still in use via email. If you receive a message asking for your email account details, delete it without response.
- Email is signed off with “Office365 Edu.” Microsoft will also never request details of your password by email or ask you if your account is still in use via email.
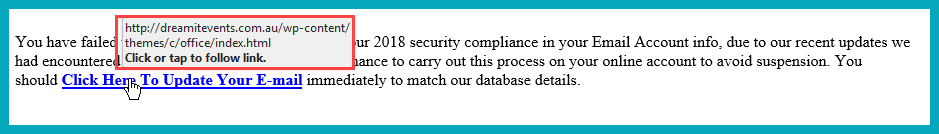
Hovering over the link reveals the URL, which in this case we can see that it is not related to NUIG at all.
Example 11: Links Asking You to Log in
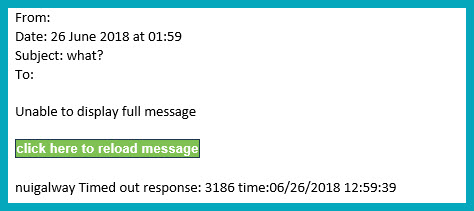
- Information Solutions and Services (ISS) DO NOT and WILL NEVER request details of your password by email or ask you if your account is still in use via email. If you receive a message asking for your email account details, delete it without response.
- This message is also very vague and doesn't give many details. Be particularly wary of any emails that are vague or give very few details with just an external link.
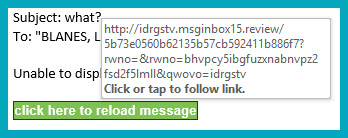
Hovering over the link reveals the URL, which in this case we can see that it is not related to NUIG at all.
Example 11: Fake Login Screens
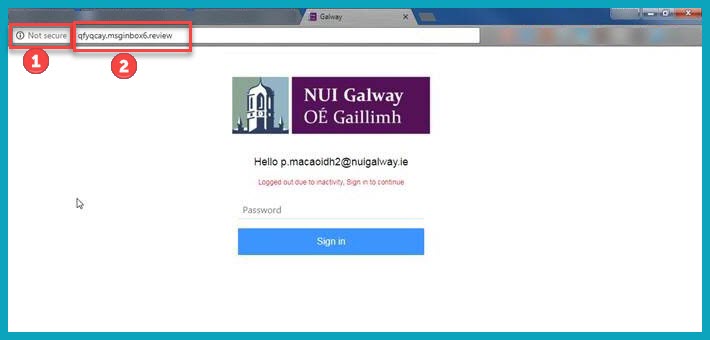
1. Web Browser Security ranks this website as "Not Secure". It is unsafe to browse any website that is not marked secure and you should never insert any credentials or passwords onto a "Not Secure" website.
2. Looking at the website address we can clearly see that this is not an NUIG website. This is the easiest way to notice a fake website that is trying to disguise itself as a legitimite site.
Example 12: SharePoint Based Phishing Scam
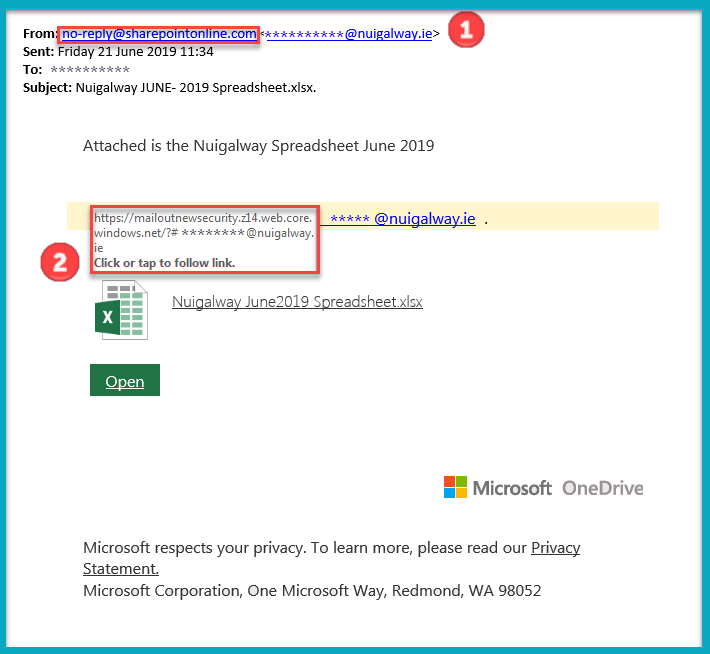
1. We have seen examples of SharePoint being used as a vehicle to send phishing links. In this example, the mail has come from a legitimate Microsoft address (no-reply@sharepointonline.com) but the link contained within it points to an illegitimate site.
2. Always hover over the link to see where it brings you before clicking on it.
3. In this case, the link brings us out to a frandulent NUI Galway email login page.
Phishing Awareness - Top Tips
You may wish to display a poster in your area to raise awareness about phishing. The below poster has been provided by HEAnet.